For the past two days, secure email provider ProtonMail has been fighting off DDoS attacks that have visibly affected the company’s services, causing short but frequent outages at regular intervals.
“The attacks went on for several hours, although the outages were far more brief, usually several minutes at a time with the longest outage on the order of 10 minutes,” a ProtonMail spokesperson said describing the attacks.
The email provider claims to “have traced the attack back to a group that claims to have ties to Russia,” a statement that some news outlets took at face value and ran stories misleading readers into thinking this was some kind of nation-state-planned cyber-attack.
But in reality, the DDoS attacks have no ties to Russia, weren’t even planned to in the first place, and the group behind the attacks denounced being Russian, to begin with.
Small hacker group behind ProtonMail DDoS attacks
Responsible for the attacks is a hacker group named Apophis Squad. In a private conversation with Bleeping Computer today, one of the group’s members detailed yesterday’s chain of events.
The Apophis member says they targeted ProtonMail at random while testing a beta version of a DDoS booter service the group is developing and preparing to launch.
The group didn’t cite any reason outside “testing” for the initial and uncalled for attack on ProtonMail, which they later revealed to have been a 200 Gbps SSDP flood, according to one of their tweets.
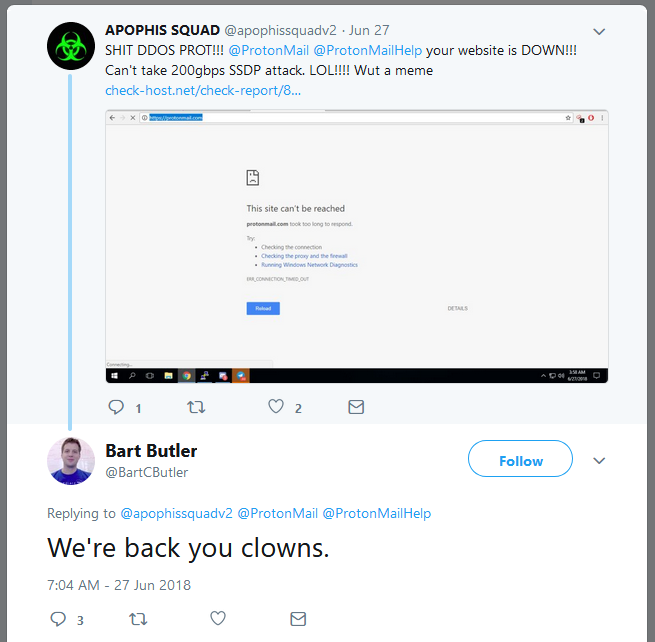
“After we sent the first attack, we downed it for 60 seconds,” an Apophis Squad member told us. He said the group didn’t intend to harass ProtonMail all day yesterday or today but decided to do so after ProtonMail’s CTO, Bart Butler, responded to one of their tweets calling the group “clowns.”
This was a questionable response on the part of the ProtonMail CTO, as it set the hackers against his company even more.
“So we then downed them for a few hours,” the Apophis Squad member said. Subsequent attacks included a whopping TCP-SYN flood estimated at 500 Gbps, as claimed by the group…
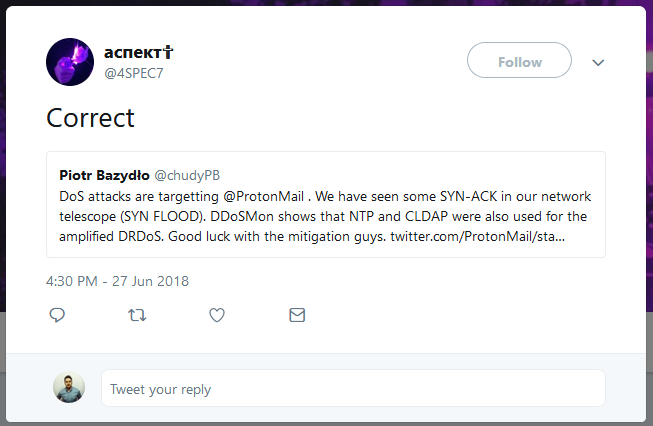
…and NTP and CLDAP floods, as observed by a security researcher at NASK and confirmed by another Apophis Squad member.
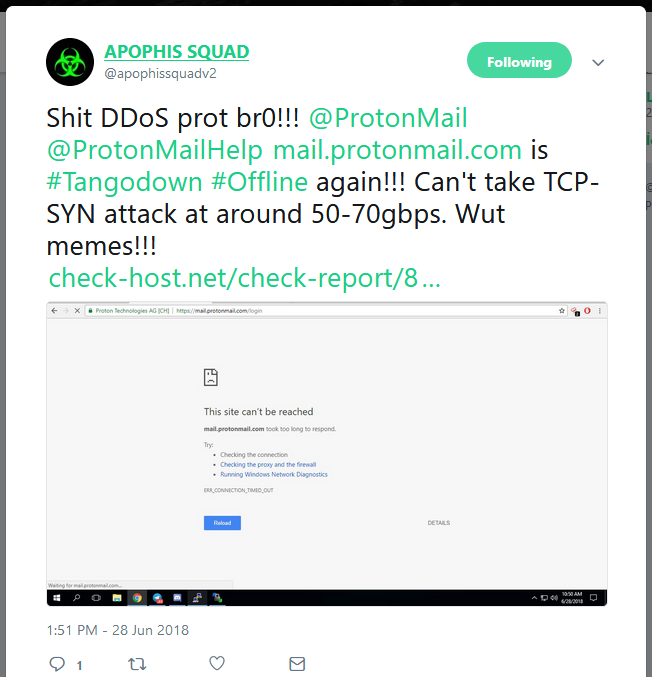
The attacks also continued today when the group launched another DDoS attack consisting of a TCP-SYN flood estimated at between 50 and 70 Gbps…
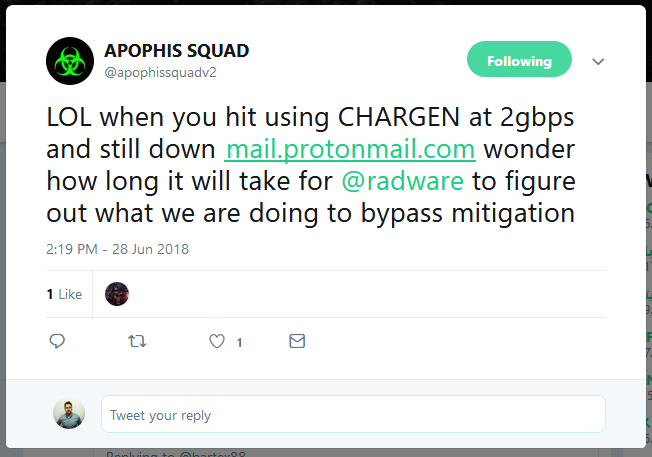
… and another CHARGEN flood estimated at 2 Gbps.
Radware, the company which was involved in mitigating the attacks on ProtonMail’s infrastructure, could not confirm the 500 Gbps DDoS attack at the time of writing but confirmed the multi-vector assault.
“We can’t confirm attack size as it varied at different points in the attack,” a Radware spokesperson said. “However we can confirm that the attack was high volumetric, multi-vector attack. It included several UDP reflection attacks, multiple TCP bursts, and Syn floods.”
In addition to targeting ProtonMail, the group also targeted Tutanota, for unknown reasons, but these attacks stopped shortly after. Tutanota execs not goading the hackers might have played a role.
Hackers deny Russian connection
The Apophis Squad group is by no means a sophisticated threat. They are your typical 2018 hacker group that hangs out in Discord channels and organizes DDoS attacks for, sometimes, childish reasons.
The group is currently developing a DDoS booter service, which they were advertising prior to yesterday’s attacks on Twitter and on Discord, claiming to be able to launch DDoS attacks using protocols such as NTP, DNS, SSDP, Memcached, LDAP, HTTP, CloudFlare bypass, VSE, ARME, Torshammer, and XML-RPC.
Their Twitter timeline claims the group is based in Russia, and so does their domain, but in a private conversation the group said this wasn’t accurate.
“We aint russian [sic],” the group told us.
“We believe the attackers to be based in the UK,” a Radware spokesperson told Bleeping Computer via email today.
If the ProtonMail DDoS attack later proves to have been of 500 Gbps, it will be one of the biggest DDoS attacks recorded, following similar DDoS attacks of 1.7 Tbps (against a yet to be named US service provider) and 1.3 Tbps (against GitHub).
Source: ProtonMail DDoS Attacks Are a Case Study of What Happens When You Mock Attackers

Robin Edgar
Organisational Structures | Technology and Science | Military, IT and Lifestyle consultancy | Social, Broadcast & Cross Media | Flying aircraft