This is called a bank error in your favour. You are liable to return the money, and you should not spend it or use it. But the bank is not allowed to just grab the money from your account. And here is part of the problem: crypto exchanges are not under the same legal restrictions as banks, which allows them to just access your accounts with relative impunity.
Earlier today, reports surfaced regarding a jaw-dropping clerical error at South Korean crypto exchange Bithumb regarding a promotional reward being sent to some customers. According to some early accounts, the reward was supposed to be 2,000 Korean won, but the users were sent 2,000 bitcoin instead. At current prices, this amounts to a roughly $140 million giveaway. That would be bad. But it was apparently much worse.
Bithumb itself has confirmed the error and indicated 620,000 bitcoin (worth around $43 billion) was accidentally sent to 695 users. The amount was large enough to cause a temporary 10% downtick in the price of bitcoin on the exchange, as some of the customers who received the misallocated funds immediately sold them. According to Bithumb, further damage was avoided by limiting withdrawals and transactions for the affected customers, and 99.7% of the errantly sent bitcoin has been recovered.
“We would like to clarify that this matter has nothing to do with external hacking or security breaches, and there are no problems with system security or customer asset management,” reads a translated version of Bithumb’s post on the matter.
The massive amount of bitcoin handed out to Bithumb customers also brings the concept of “paper bitcoin” to the forefront, as the reality is these exchanges do not necessarily have all of the bitcoin to back the amounts shown to their respective customers. This issue was at the heart of the infamous collapse of early bitcoin exchange Mt. Gox in 2014, which was by far the largest crypto exchange at the time. According to blockchain data provider Arkham Intelligence, Bithumb has roughly $5.3 billion in assets, which is nowhere near the $43 billion it says it errantly awarded to some of its customers.
[…]
Source: South Korean Crypto Exchange Accidentally Gave Away $43 Billion Worth of Paper Bitcoin













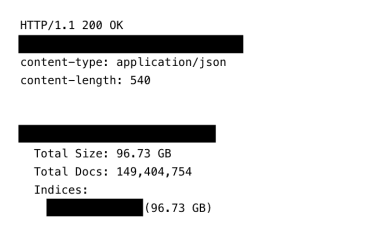 This screenshot shows the total count of records and size of the exposed infostealer database.
This screenshot shows the total count of records and size of the exposed infostealer database.