the addresses and demographic details of more than 80 million US households were exposed on an unsecured database stored on the cloud, independent security researchers have found.
The details included names, ages and genders as well as income levels and marital status. The researchers, led by Noam Rotem and Ran Locar, were unable to identify the owner of the database, which until Monday was online and required no password to access. Some of the information was coded, like gender, marital status and income level. Names, ages and addresses were not coded.
The data didn’t include payment information or Social Security numbers. The 80 million households affected make up well over half of the households in the US, according to Statista.
“I wouldn’t like my data to be exposed like this,” Rotem said in an interview with CNET. “It should not be there.”
Rotem and his team verified the accuracy of some data in the cache but didn’t download the data to minimize the invasion of privacy of those listed, he said.
[…]
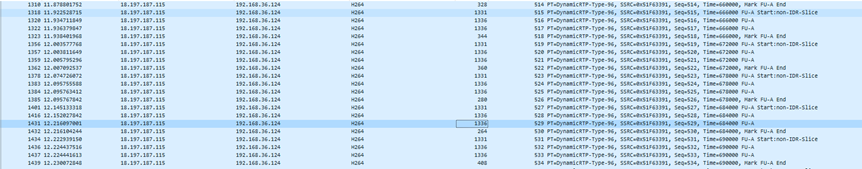
Unlike a hack, you don’t need to break into a computer system to access an exposed database. You simply need to find the IP address, the numerical code assigned to any given web page.
[…]
Rotem found that the data was stored on a cloud service owned by Microsoft. Securing the data is up to the organization that created the database, and not Microsoft itself.
“We have notified the owner of the database and are taking appropriate steps to help the customer remove the data until it can be properly secured,” a Microsoft spokesperson told CNET in a statement Monday.
The server hosting the data came online in February, Rotem found, and he discovered it in April using tools he developed to search for and catalog unsecured databases.
Source: Cloud database removed after exposing details on 80 million US households – CNET