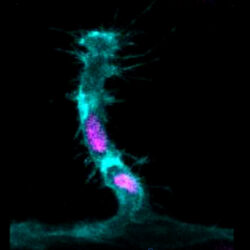
Scientists rewrite 100 year old textbooks on how cells divide
Scientists from The University of Manchester have changed our understanding of how cells in living organisms divide, which could revise what students are taught at school. In a Wellcome funded study published today (01/05/25) in Science – one of the world’s leading scientific journals – the researchers challenge conventional wisdom taught in schools for over Read more about Scientists rewrite 100 year old textbooks on how cells divide[…]