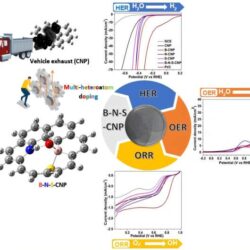
Turning car exhausts into power: New method transforms carbon nanoparticles from emissions into renewable energy catalysts
We have developed a breakthrough method to convert carbon nanoparticles (CNPs) from vehicular emissions into high-performance electrocatalysts. This innovation provides a sustainable approach to pollution management and energy production by repurposing harmful particulate matter into valuable materials for renewable energy applications. Our work, published in Carbon Neutralization, addresses both environmental challenges and the growing demand Read more about Turning car exhausts into power: New method transforms carbon nanoparticles from emissions into renewable energy catalysts[…]