researchers have shown that it’s possible to clone these devices, as reported by Hackster.io.
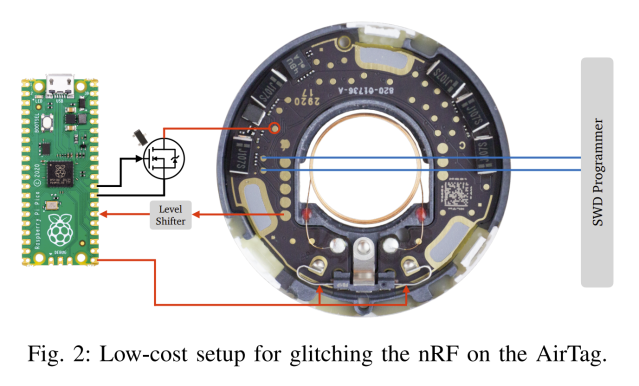
The research paper explains the cloning process, which requires physical access to the hardware. To achieve the hack, the Nordic nRF52832 inside the AirTag must be voltage glitched to enable its debug port. The researchers were able to achieve this with relatively simple tools, using a Pi Pico fitted with a few additional components.
With the debug interface enabled, it’s simple to extract the microcontroller’s firmware. It’s then possible to clone this firmware onto another tag. The team also experimented with other hacks, like having the AirTag regularly rotate its ID to avoid triggering anti-stalking warnings built into Apple’s tracing system.
As the researchers explain, it’s clear that AirTags can’t really be secure as long as they’re based on a microcontroller that is vulnerable to such attacks. It’s not the first AirTag cloning we’ve seen either. They’re an interesting device with some serious privacy and safety implications, so it pays to stay abreast of developments in this area.
[…]
Source: Apple AirTags Hacked And Cloned With Voltage Glitching | Hackaday

Robin Edgar
Organisational Structures | Technology and Science | Military, IT and Lifestyle consultancy | Social, Broadcast & Cross Media | Flying aircraft