Chinese researchers say they successfully bypassed fingerprint authentication safeguards on smartphones by staging a brute force attack.
Researchers at Zhejiang University and Tencent Labs capitalized on vulnerabilities of modern smartphone fingerprint scanners to stage their break-in operation, which they named BrutePrint. Their findings are published on the arXiv preprint server.
A flaw in the Match-After-Lock feature, which is supposed to bar authentication activity once a device is in lockout mode, was overridden to allow a researcher to continue submitting an unlimited number of fingerprint samples.
Inadequate protection of biometric data stored on the Serial Peripheral Interface of fingerprint sensors enables attackers to steal fingerprint images. Samples also can be easily obtained from academic datasets or from biometric data leaks.
[…]
All Android devices and one HarmonyOS (Huawei) device tested by researchers had at least one flaw allowing for break-ins. Because of tougher defense mechanisms in IOS devices, specifically Apple iPhone SE and iPhone 7, those devices were able to withstand brute-force entry attempts. Researchers noted that iPhone devices were susceptible to CAMF vulnerabilities, but not to the extent that successful entry could be achieved.
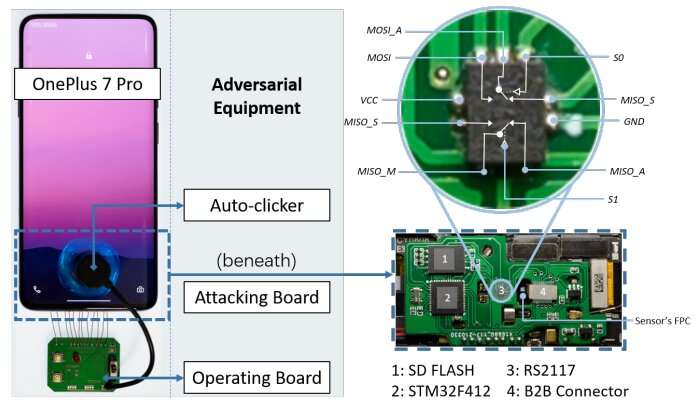
To launch a successful break-in, an attacker requires physical access to a targeted phone for several hours, a printed circuit board easily obtainable for $15, and access to fingerprint images.
Fingerprint databases are available online through academic resources, but hackers more likely will access massive volumes of images obtained through data breaches.
[…]
More information: Yu Chen et al, BrutePrint: Expose Smartphone Fingerprint Authentication to Brute-force Attack, arXiv (2023). DOI: 10.48550/arxiv.2305.10791
Source: Brute-force test attack bypasses Android biometric defense

Robin Edgar
Organisational Structures | Technology and Science | Military, IT and Lifestyle consultancy | Social, Broadcast & Cross Media | Flying aircraft