Attacks come in two main forms: one is scanning the drive for memory dumps and the other is by sniffing the bitlocker key through RAM dumping on cold boots.
Cold Boot Attacks
Introductory blog post
Frequently asked questions
Experiment guide
Source code
Source: Lest We Remember: Cold Boot Attacks on Encryption Keys
Over time there have been many different physical attacks against full disk encryption, such as Cold Boot attacks [0][1] that we have previously researched. In addition, various attacks based on TPM interface sniffing [2] or DMA [3] have been used to gain access to an encryption key.
[…]
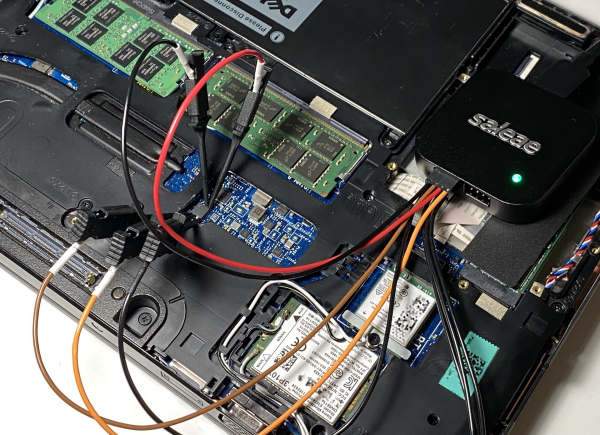
I captured the SPI signals with the Saleae Logic Pro 8 logic analyzer, which is capable of recording four signals up to 100 MHz. The wide terminal pitch of SOIC-8 package allows an effortless way to hook the probes, and the whole capture process can be performed under one minute.
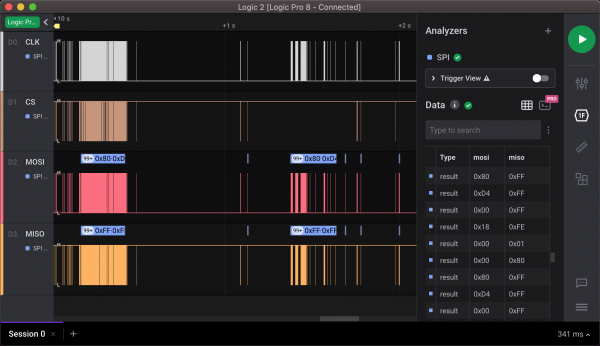
The Logic 2 application supports SPI decoding out-of-the-box. The only caveat is to remember that the SS-line is inverted. Fortunately, the decoding options of Saleae allow us to choose whether the chip is selected when the SS-line is high or low. The screenshot below shows decoded MOSI and MISO byte streams from the capture.
[…]
Even though Proof of Concepts are awesome, proper weaponizing usually takes the attack to a whole new level, and as we stated at the beginning of this post, the real advantage comes if this can be performed with minimal effort. Therefore, I decided to automate the attack process as far as possible. The toolchain consists of the following parts:
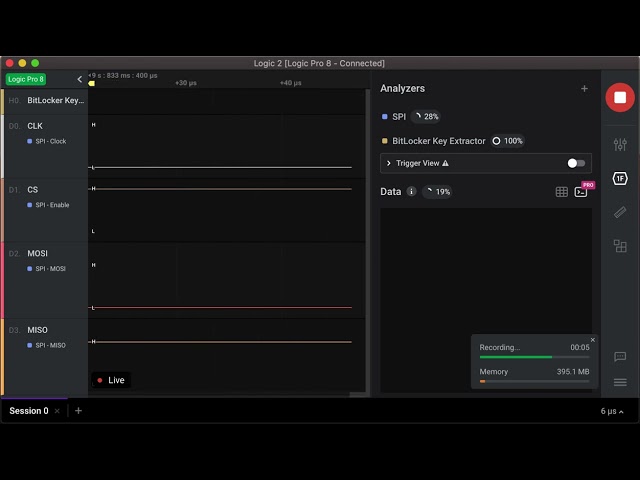
- Custom High-Level Analyzer for searching VMK entries from TPM transactions.
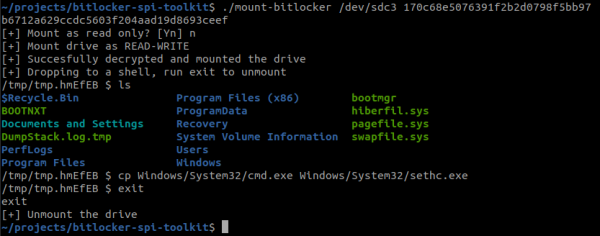
- Docker container, which includes all the necessary tools to mount the drive just by giving VMK.
The workflow with the tooling is as follows:
- Sniff the SPI bus and extract VMK.
- Remove the drive and attach it to the attacker’s machine or boot the target directly from a USB-stick if allowed.
- Decrypt and mount the drive.
The video below show how the analyzer is able to extract the VMK from the sniffed data. The key can be then passed to the mount tool which decrypts the content and drops you to a shell where you are able to modify the volume content.
You can find the above tooling on GitHub.
Source: Sniff, there leaks my BitLocker key
TLDR: You can sniff BitLocker keys in the default config, from either a TPM1.2 or TPM2.0 device, using a dirt cheap FPGA (~$40NZD) and now publicly available code, or with a sufficiently fancy logic analyzer. After sniffing, you can decrypt the drive. Don’t want to be vulnerable to this? Enable additional pre-boot authentication.
Source: Extracting BitLocker keys from a TPM
Scanning RAM dumps / hiberyfile.sys
Volatility is a framework for memory analysis and forensics. The Volatility plugin: BitLocker allows you to retrieves the Full Volume Encryption Key (FVEK) in memory. The FVEK can then be used with Dislocker to decrypt the volume. This plugin has been tested on every 64-bit Windows version from Windows 7 to Windows 10 and is fully compatible with Dislocker.
Elcomsoft Forensic Disk Decryptor is a commercial (and expensive!) way to automate the use of this tooling. Instantly access data stored in encrypted BitLocker, FileVault 2, PGP Disk, TrueCrypt and VeraCrypt disks and containers. The tool extracts cryptographic keys from RAM captures, hibernation and page files or uses plain-text password or escrow keys to decrypt files and folders stored in crypto containers or mount encrypted volumes as new drive letters for instant, real-time access.
Supports: BitLocker (including TPM configurations), FileVault 2 (including APFS volumes), LUKS, PGP Disk, TrueCrypt and VeraCrypt encrypted containers and full disk encryption, BitLocker To Go, XTS-AES BitLocker encryption, Jetico BestCrypt, RAM dumps, hibernation files, page files
They do offer a trial version and the current version seems to be 2.20.1011

Robin Edgar
Organisational Structures | Technology and Science | Military, IT and Lifestyle consultancy | Social, Broadcast & Cross Media | Flying aircraft
