Back in March 2019, Amnesty International published a report that uncovered a targeted attack against journalists and human rights activists in Egypt. The victims even received an e-mail from Google warning them that government-backed attackers attempted to steal their passwords.
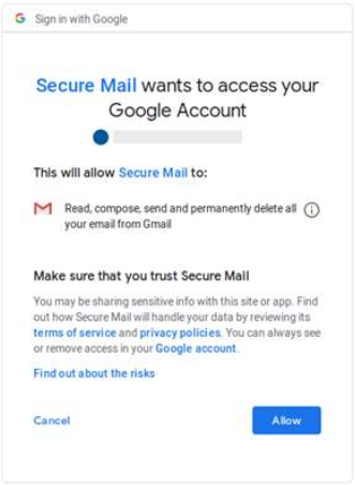
According to the report, the attackers did not rely on traditional phishing methods or credential-stealing payloads, but rather utilized a stealthier and more efficient way of accessing the victims’ inboxes: a technique known as “OAuth Phishing”. By abusing third-party applications for popular mailing services such as Gmail or Outlook, the attackers manipulated victims into granting them full access to their e-mails.
Fig 1: Previous OAuth phishing campaign
Recently, we were able to find previously unknown or undisclosed malicious artifacts belonging to this operation. A new website we attributed to this malicious activity revealed that the attackers are going after their prey in more than one way, and might even be hiding in plain sight: developing mobile applications to monitor their targets, and hosting them on Google’s official Play Store.
After we notified Google about the involved applications, they quickly took them off of the Play Store and banned the associated developer.
Infrastructure: The Early Days
The full list of indicators belonging to this campaign and shared by Amnesty on GitHub showed multiple websites that used keywords such as “mail”, “secure”, or “verify”, possibly not to arouse any suspicions and to masquerade as legitimate mailing services.
By visualizing the information available about each of these websites, we saw clear connections between them: they were registered using NameCheap, had HTTPS certificates, and many of them resolved to the same IP addresses.
The addresses shared the same IPv4 range or netblock (185.125.228[.]0/22), which belongs to a Russian telecommunications company called MAROSNET.
Fig 2: Maltego visualization of campaign infrastructure
Naturally, the websites cannot be accessed nowadays, but by looking over public scans available for some of them we could see that in addition to being related to OAuth phishing, they hosted phishing pages that impersonated Outlook or Facebook and tried to steal log-in credentials for those services
[…]
Following up on the investigation first conducted by Amnesty International, we revealed new aspects of the attack that has been after Egypt’s civil society since at least 2018.
Whether it is phishing pages, legitimate-looking applications for Outlook and Gmail, and mobile applications to track a device’s communications or location, it is clear that the attackers are constantly coming up with creative and versatile methods to reach victims, spy on their accounts, and monitor their activity.
We discovered a list of victims that included handpicked political and social activists, high-profile journalists and members of non-profit organizations in Egypt.
The information we gathered from our investigation suggested that the perpetrators are Arabic speakers, and well familiar with the Egyptian ecosystem. Because the attack might be government-backed, it means that we are looking at what might be a surveillance operation of a country against its own citizens or of another government that screens some other attack using this noisy one.
Source: The Eye on the Nile – Check Point Research

Robin Edgar
Organisational Structures | Technology and Science | Military, IT and Lifestyle consultancy | Social, Broadcast & Cross Media | Flying aircraft