I was reticent to write this blog post because it leaves a lot of questions unanswered, questions that we should be able to answer. It’s about a data breach with almost 90GB of personal information in it across tens of millions of records – including mine. Here’s what I know:
Back in Feb, Dehashed reached out to me with a massive trove of data that had been left exposed on a major cloud provider via a publicly accessible Elasticsearch instance. It contained 103,150,616 rows in total, the first 30 of which look like this:
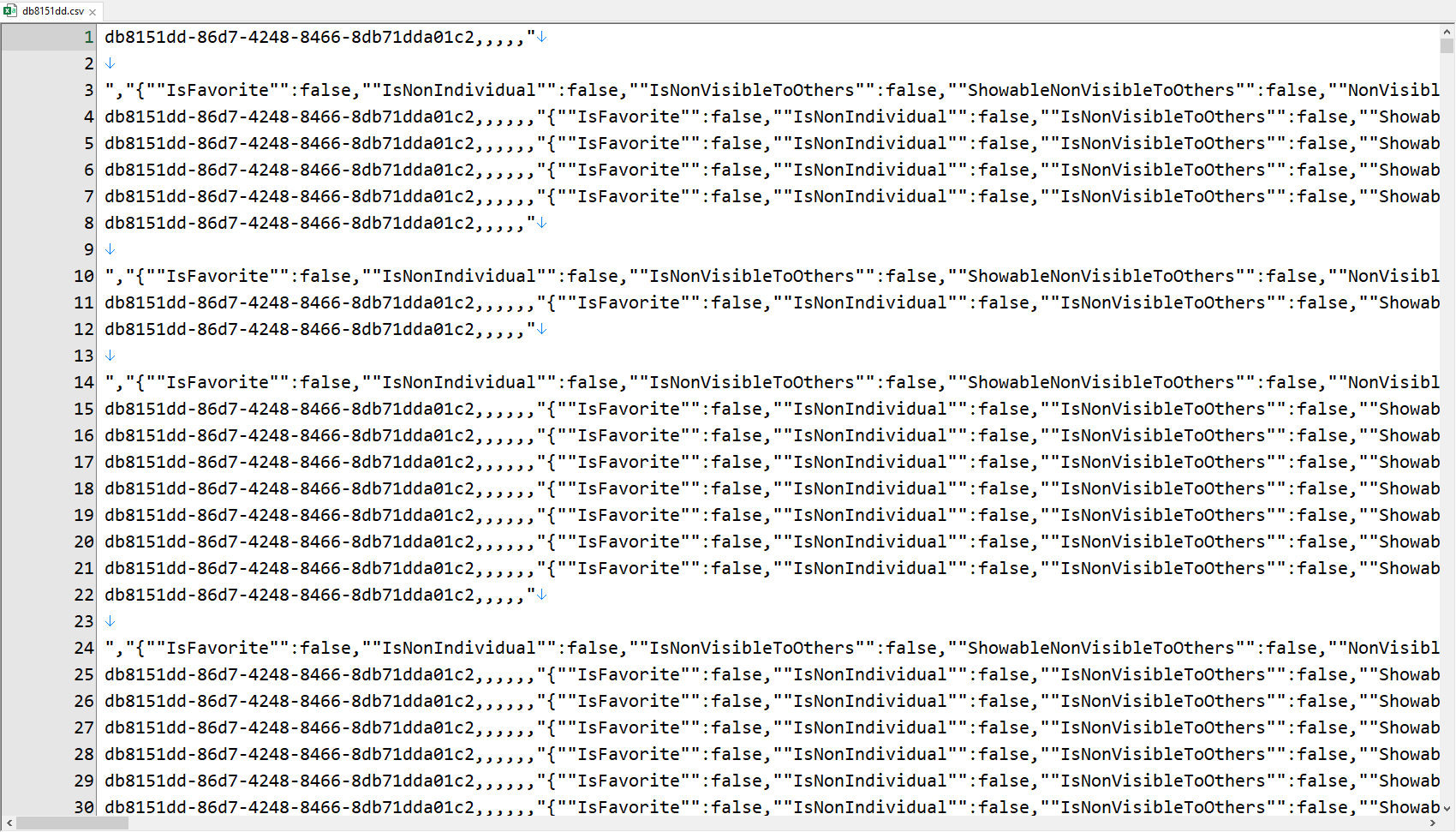
The global unique identifier beginning with “db8151dd” features heavily on these first lines hence the name I’ve given the breach. I’ve had to give it this name because frankly, I’ve absolutely no idea where it came from, nor does anyone else I’ve worked on with this.
It’s mostly scrapable data from public sources, albeit with some key differences. Firstly, my phone number is not usually exposed and that was in there in full. Yes, there are many places that (obviously) have it, but this isn’t a scrape from, say, a public LinkedIn page. Next, my record was immediately next to someone else I’ve interacted with in the past as though the data source understood the association. I found that highly unusual as it wasn’t someone I’d expect to see a strong association with and I couldn’t see any other similar folks. But it’s the next class of data in there which makes this particularly interesting and I’m just going to quote a few snippets here:
Recommended by Andie [redacted last name]. Arranged for carpenter apprentice Devon [redacted last name] to replace bathroom vanity top at [redacted street address], Vancouver, on 02 October 2007.
Met at the 6th National Pro Bono Conference in Ottawa in September 2016
Met on 15-17 October 2001 in Vancouver for the Luscar/Obed/Coal Valley arbitration.
It feels like a CRM. These are records of engagement the likes you’d capture in order to later call back to who had been met where and what they’d done. It wasn’t just simple day to day business interaction stuff either, there was also this:
But then there’s also a bunch of legal summaries, for example “CASE CLOSING SUMMARY ON USA V. [redacted]” and “10/3/11 detention hrg in court 20 min plus travel split with [redacted]”— Troy Hunt (@troyhunt) February 23, 2020
But nowhere – absolutely nowhere – was there any indication of where the data had originated from. The closest I could get to that at all was the occurrence of the following comments which appeared over and over again:
This contact information was synchronized from Exchange. If you want to change the contact information, please open OWA and make your changes there.
Exported from Microsoft Outlook (Do not delete)
Contact Created By Evercontact
Evercontact did actually reach out and we discussed the breach privately but it got us no closer to a source. I communicated with multiple infosec journalists (one of whose own personal data was also in the breach) and still, we got no closer. Over the last 3 months I kept coming back to this incident time and time again, looking at the data with fresh eyes and each time, coming up empty. And just before you ask, no, cloud providers won’t disclose which customer owns an asset but they will reach out to those with unsecured assets.
Today is the end of the road for this breach investigation and I’ve just loaded all 22,802,117 email addresses into Have I Been Pwned. Why load it at all? Because every single time I ask about whether I should add data from an unattributable source, the answer is an overwhelming “yes”:
If I have a MASSIVE spam list full of personal data being sold to spammers, should I load it into @haveibeenpwned?— Troy Hunt (@troyhunt) November 15, 2016
So, mark me down for another data breach of my own personal info. There’s nothing you nor I can do about it beyond being more conscious than ever about just how far our personal information spreads without our consent and indeed, without our knowledge. And, perhaps most alarmingly, this is far from the last time I’ll be writing a blog post like this.
Edit 1: No, I don’t load complete and individual records into HIBP, only email addresses. As such, only the presence of an address is searchable, the data associated with the address is not stored nor retrievable.
Edit 2: No, I can’t manually trawl through 100M+ records and extract yours out.
Edit 3: Thanks to some community sleuthing, the origin of this breach has now been identified as the Covve contacts app. Their public disclosure is in that link and they’ve also been in contact with regulators and had a couple of phone calls with myself.

Robin Edgar
Organisational Structures | Technology and Science | Military, IT and Lifestyle consultancy | Social, Broadcast & Cross Media | Flying aircraft
