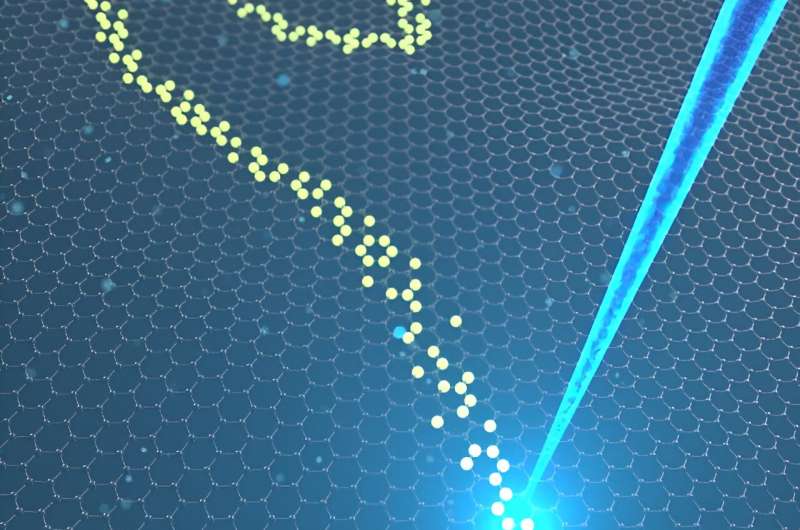
Scientists from Duke-NUS Medical School and the University of California, Santa Cruz, have discovered the secret to regulating our internal clock. They identified that this regulator sits right at the tail end of Casein Kinase 1 delta (CK1δ), a protein which acts as a pace setter for our internal biological clock or the natural 24-hour cycles that control sleep-wake patterns and other daily functions, known as circadian rhythm.
Published in the journal PNAS, their findings could pave the way for new approaches to treating disorders related to our body clock.
CK1δ regulates circadian rhythms by tagging other proteins involved in our biological clock to fine-tune the timing of these rhythms. In addition to modifying other proteins, CK1δ itself can be tagged, thereby altering its own ability to regulate the proteins involved in running the body’s internal clock.
[…]
“Our findings pinpoint to three specific sites on CK1δ’s tail where phosphate groups can attach, and these sites are crucial for controlling the protein’s activity. When these spots get tagged with a phosphate group, CK1δ becomes less active, which means it doesn’t influence our circadian rhythms as effectively. Using high-resolution analysis, we were able to pinpoint the exact sites involved — and that’s really exciting.”
[…]
We found that the δ1 tail interacts more extensively with the main part of the protein, leading to greater self-inhibition compared to δ2. This means that δ1 is more tightly regulated by its tail than δ2. When these sites are mutated or removed, δ1 becomes more active, which leads to changes in circadian rhythms. In contrast, δ2 does not have the same regulatory effect from its tail region.”
This discovery highlights how a small part of CK1δ can greatly influence its overall activity. This self-regulation is vital for keeping CK1δ activity balanced, which, in turn, helps regulate our circadian rhythms.
The study also addressed the wider implications of these findings. CK1δ plays a role in several important processes beyond circadian rhythms, including cell division, cancer development, and certain neurodegenerative diseases. By better understanding how CK1δ’s activity is regulated, scientists could open new avenues for treating not just circadian rhythm disorders but also a range of conditions.
[…]
“Regulating our internal clock goes beyond curing jet lag — it’s about improving sleep-quality, metabolism and overall health. This important discovery could potentially open new doors for treatments that could transform how we manage these essential aspects of our daily lives.”
The researchers plan to further investigate how real-world factors, such as diet and environmental changes, affect the tagging sites on CK1δ.
[…]
Story Source:
Materials provided by Duke-NUS Medical School. Note: Content may be edited for style and length.
Journal Reference:
- Rachel L. Harold, Nikhil K. Tulsian, Rajesh Narasimamurthy, Noelle Yaitanes, Maria G. Ayala Hernandez, Hsiau-Wei Lee, Priya Crosby, Sarvind M. Tripathi, David M. Virshup, Carrie L. Partch. Isoform-specific C-terminal phosphorylation drives autoinhibition of Casein kinase 1. Proceedings of the National Academy of Sciences, 2024; 121 (41) DOI: 10.1073/pnas.2415567121