Last April, Steven Schoen received an email from someone named Natalie Andrea who said she worked for a company called We Purchase Apps. She wanted to buy his Android app, Emoji Switcher. But right away, something seemed off.
“I did a little bit of digging because I was a little sketched out because I couldn’t really find even that the company existed,” Schoen told BuzzFeed News.
The We Purchase Apps website listed a location in New York, but the address appeared to be a residence. “And their phone number was British. It was just all over the place,” Schoen said.
It was all a bit weird, but nothing indicated he was about to see his app end up in the hands of an organization responsible for potentially hundreds of millions of dollars in ad fraud, and which has funneled money to a cabal of shell companies and people scattered across Israel, Serbia, Germany, Bulgaria, Malta, and elsewhere.
Schoen had a Skype call with Andrea and her colleague, who said his name was Zac Ezra, but whose full name is Tzachi Ezrati. They agreed on a price and to pay Schoen up front in bitcoin.
“I would say it was more than I had expected,” Schoen said of the price. That helped convince him to sell.
A similar scenario played out for five other app developers who told BuzzFeed News they sold their apps to We Purchase Apps or directly to Ezrati. (Ezrati told BuzzFeed News he was only hired to buy apps and had no idea what happened to them after they were acquired.)
“A significant portion of the millions of Android phone owners who downloaded these apps were secretly tracked as they scrolled and clicked inside the application.”But an investigation by BuzzFeed News reveals that these seemingly separate apps and companies are today part of a massive, sophisticated digital advertising fraud scheme involving more than 125 Android apps and websites connected to a network of front and shell companies in Cyprus, Malta, British Virgin Islands, Croatia, Bulgaria, and elsewhere. More than a dozen of the affected apps are targeted at kids or teens, and a person involved in the scheme estimates it has stolen hundreds of millions of dollars from brands whose ads were shown to bots instead of actual humans. (A full list of the apps, the websites, and their associated companies connected to the scheme can be found in this spreadsheet.)
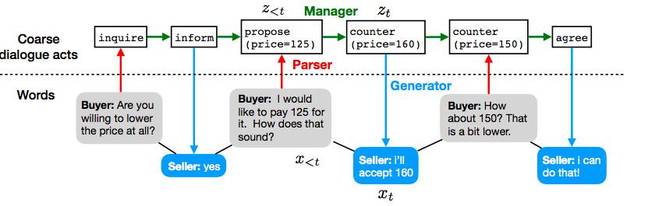
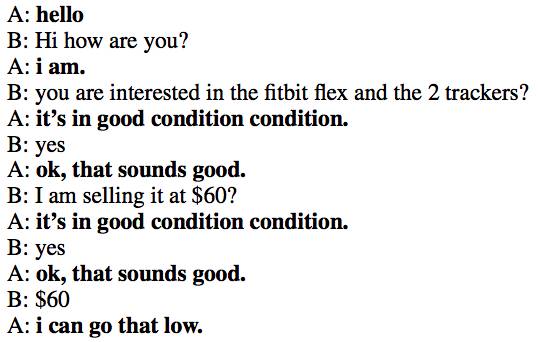
One way the fraudsters find apps for their scheme is to acquire legitimate apps through We Purchase Apps and transfer them to shell companies. They then capture the behavior of the app’s human users and program a vast network of bots to mimic it, according to analysis from Protected Media, a cybersecurity and fraud detection firm that analyzed the apps and websites at BuzzFeed News’ request.
This means a significant portion of the millions of Android phone owners who downloaded these apps were secretly tracked as they scrolled and clicked inside the application. By copying actual user behavior in the apps, the fraudsters were able to generate fake traffic that bypassed major fraud detection systems.
“This is not your run-of-the-mill fraud scheme,” said Asaf Greiner, the CEO of Protected Media. “We are impressed with the complex methods that were used to build this fraud scheme and what’s equally as impressive is the ability of criminals to remain under the radar.”
Another fraud detection firm, Pixalate, first exposed one element of the scheme in June. At the time, it estimated that the fraud being committed by a single mobile app could generate $75 million a year in stolen ad revenue. After publishing its findings, Pixalate received an email from an anonymous person connected to the scheme who said the amount that’s been stolen was closer to 10 times that amount. The person also said the operation was so effective because it works “with the biggest partners [in digital advertising] to ensure the ongoing flow of advertisers and money.”
In total, the apps identified by BuzzFeed News have been installed on Android phones more than 115 million times, according to data from analytics service AppBrain. Most are games, but others include a flashlight app, a selfie app, and a healthy eating app. One app connected to the scheme, EverythingMe, has been installed more than 20 million times.
Once acquired, the apps continue to be maintained in order to keep real users happy and create the appearance of a thriving audience that serves as a cover for the cloned fake traffic. The apps are also spread among multiple shell companies to distribute earnings and conceal the size of the operation.
Source: How A Massive Ad Fraud Scheme Exploited Android Phones To Steal Millions Of Dollars