The new standard will work as an extension to TLS, a cryptographic protocol that underpins the more widely-known HTTPS protocol, used for loading websites inside browsers via an encrypted connection.
The TLS Delegate Credentials extension was specifically developed for large website setups, such as Facebook, or for website using content delivery networks (CDNs), such as Cloudflare.
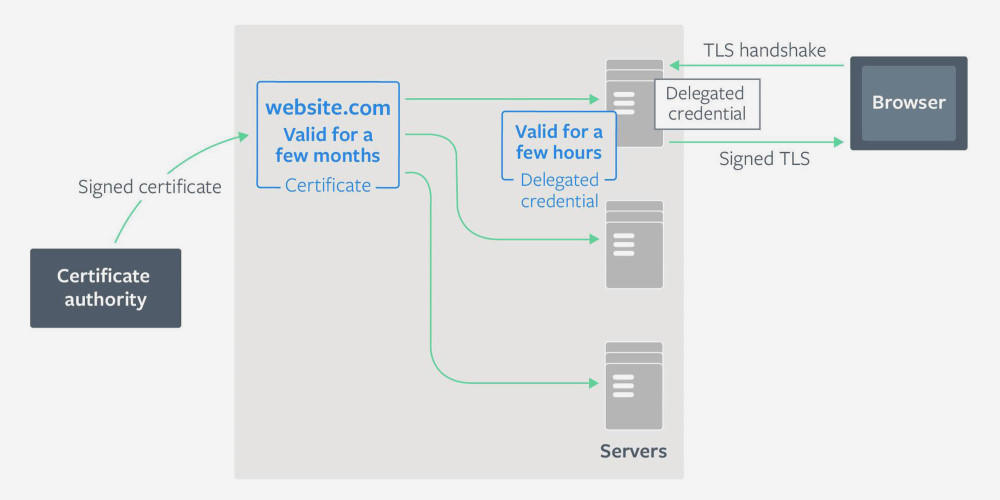
How TLS Delegate Credentials works
For example, a big website like Facebook has thousands of servers spread all over the world. In order to support HTTPS traffic on all, Facebook has to place a copy of its TLS certificate private key on each one.
This is a dangerous setup. If an attacker hacks one server and steals the TLS private key, the attacker can impersonate Facebook servers and intercept user traffic until the stolen certificate expires.
The same thing is also valid with CDN services like Cloudflare. Anyone hosting an HTTPS website on Cloudflare’s infrastructure must upload their TLS private key to Cloudflare’s service, which then distributes it to thousands of servers across the world.
The TLS Delegate Credentials extension allows site owners to create short-lived TLS private keys (called delegated credentials) that they can deploy to these multi-server setups, instead of the real TLS private key.
The delegated credentials can live up to seven days and can be rotated automatically once they expire.
TLS Delegated Credentials shortens MitM attack window
The most important security improvement that comes with this new TLS extension is that if — in the worst-case scenarios — an attacker does manage to hack a server, the stolen private key (actually a delegated credential) won’t work for more than a few days, rather than weeks, months, or even a year, as it does now.
You can read more in-depth technical explanations about the new TLS Delegated Credentials extensions on the Facebook, Mozilla, and Cloudflare blogs.
The IETF draft specification is available here. TLS Delegated Credentials will be compatible with the TLS protocol v1.3 and later.
Source: Facebook, Mozilla, and Cloudflare announce new TLS Delegated Credentials standard | ZDNet

Robin Edgar
Organisational Structures | Technology and Science | Military, IT and Lifestyle consultancy | Social, Broadcast & Cross Media | Flying aircraft